In this article, I would like to introduce to you the ATA (Microsoft Advanced Threat Analytics) which provides by Microsoft as great security capabilities, in fact, it knows as software that monitors securely your domain object activities, it learns the computer and users behaviors and reports you the details nicely on ATA dashboard, So it’s mainly gathering information about DNS, RPC, NTLM, Kerberos, RDP, Authentication, logging, abnormal behavior, security risk and more, The ATA makes port mirroring to the Domain Controller’s network adapter toward ATA gateway and checks the traffic packages.
Certainly, you have the ability to integrate the events to SYSLOG systems such as SIEM system, or use on Windows Event Forwarding.
Malicious attach detection such as:
Pass-the-Ticket (PtT)
Pass-the-Hash (PtH)
Overpass-the-Hash
Forged PAC (MS14-068)
Golden Ticket
Malicious replications
Reconnaissance
Brute Force
Remote execution
You can download it for 90 free days as a trial from the following link:
Download ATA from the Microsoft Volume Licensing Service Center or from the TechNet Evaluation Center or from MSDN.
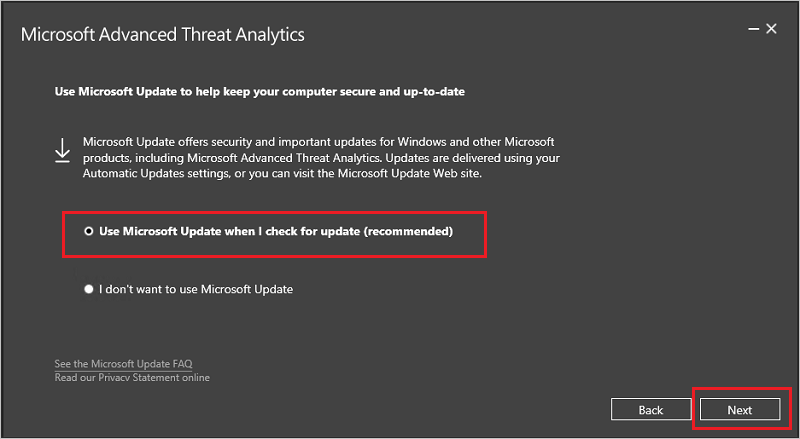
I give up the simple steps, and moving on to the installation which is pretty straightforward:
– I recommend you make sure your machine is up to date
– You can install it on the Domain Controller.
Initiate the installation wizard:
Create “Self-Signed Certificate“:

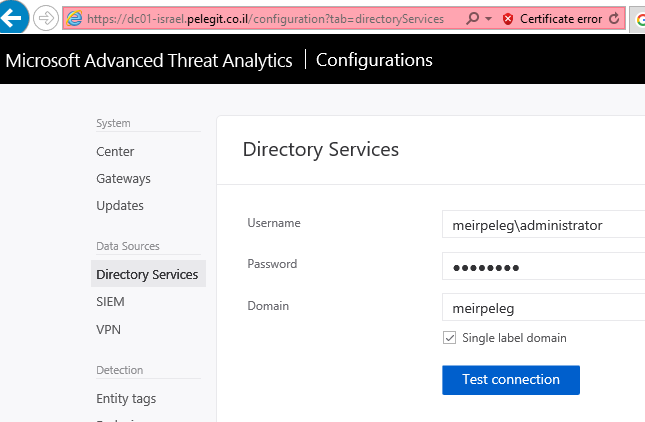
Post installation, we have to start with “ATA configuration” and peer it with our AD:
The next step is to “Download Gateway setup and install the first Gateway”:

Note:
We should check if that KB2919355 is already installed or not, run this query to verify it:
Get-HotFix -Id kb2919355
As soon as you have open the installation proceed with next until to this step:
State administrator credential:
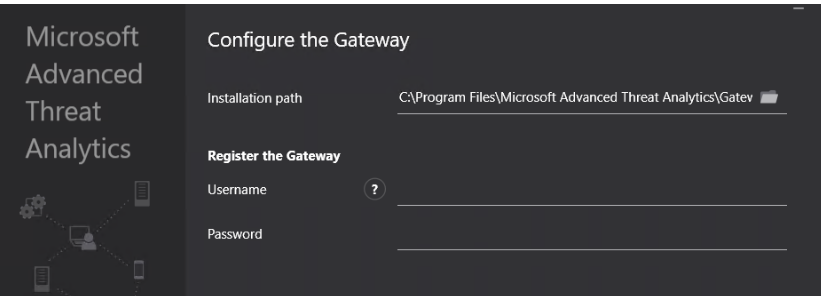
Configure the Gateway:
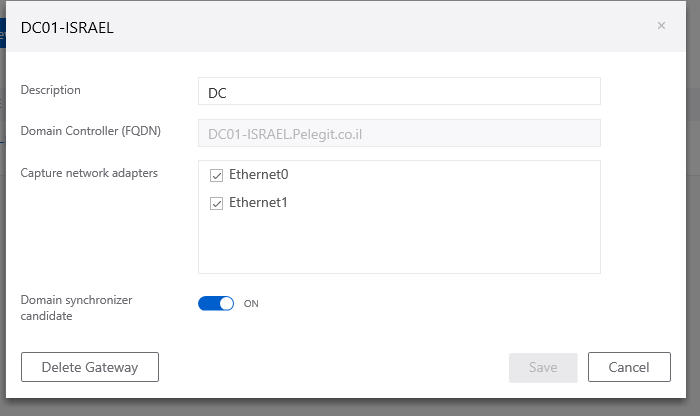
Domain synchronizer candidate– It synchronizes all events from a specific AD, if you have unchecked the domain synchronizer candidate and neither of your DC’s are enabled, the ATA detect them by monitoring traffic, if it won’t find it, take under your consideration that you won’t see any results, consequently by default al ATA gateways synchronizer candidates.
The ATA Lightweight Gateway runs every 10 seconds and dynamically updates the CPU and memory utilization, no available resources? no available results will be displayed
You can verify the port forwarding is working by going through the following article:
https://docs.microsoft.com/en-us/advanced-threat-analytics/validate-port-mirroring
You can enable the SIEM:
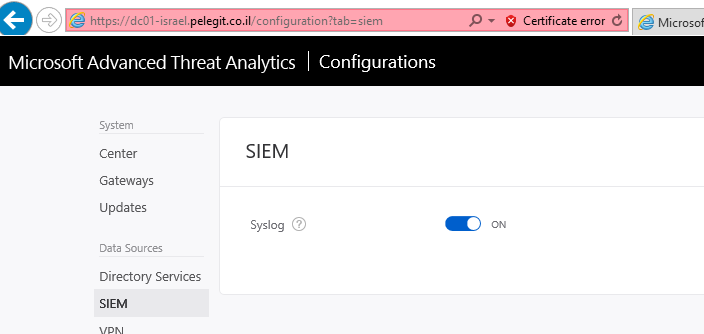
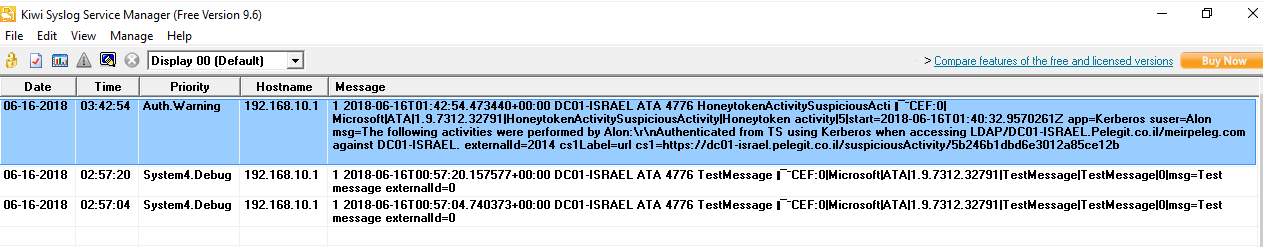
Syslog events:
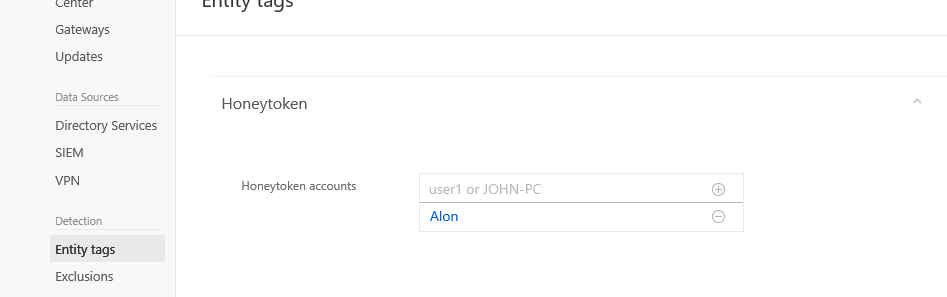
Honeytoken user:
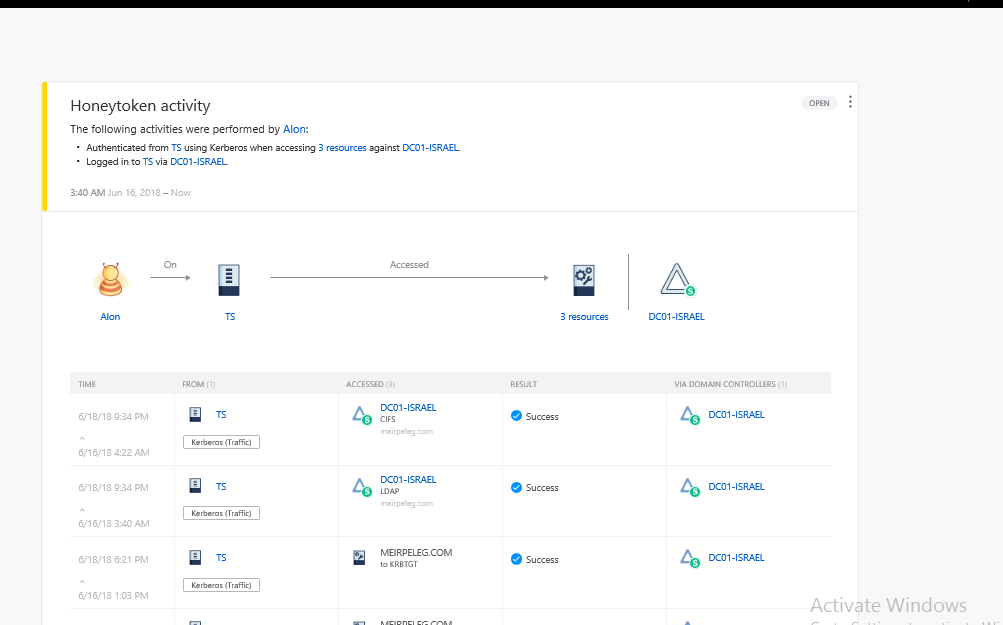
Using “Honeytoken ” we can “Track” a certain object steps, get the trace, and activities of the same user, for my opinion- great feature, a suspicious object will be traced!
Specifying user or computer object:
And retrieves any object’s movement and actions in the domain:
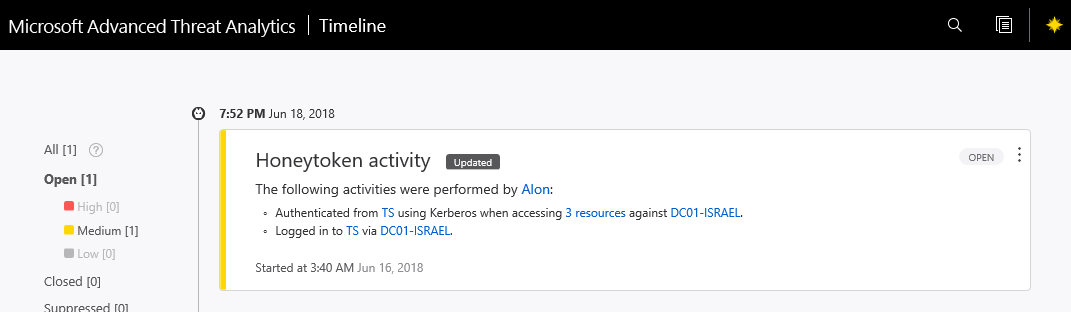
Honeytoken activity:
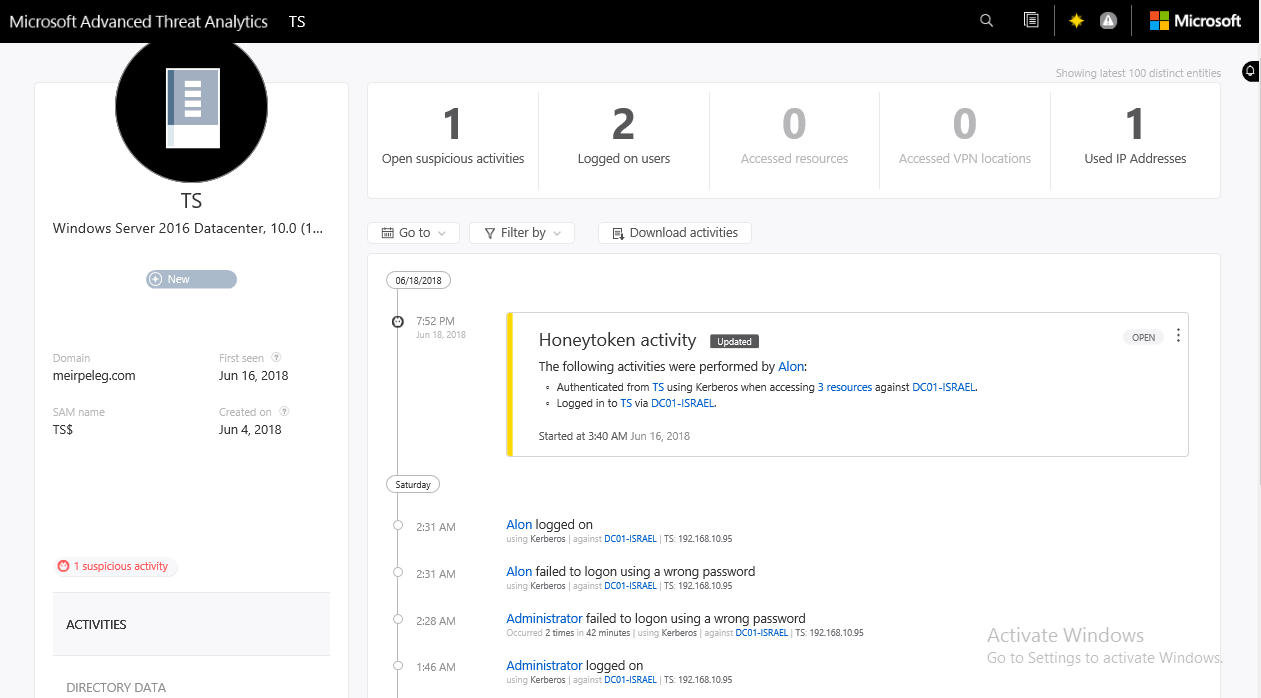
Not Only, regardless of the “Honeytoken” We can search a machine or users in the search field and get activity:
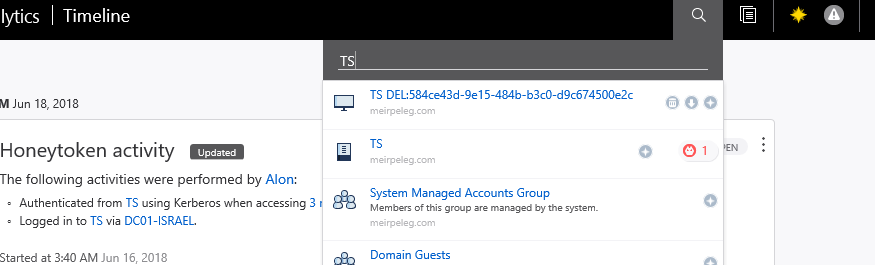
For TS machine we get the following details:
As you can see, we get the login attempt events, wrong and successful events, IP, suspicious activities, machine details, anything that happens on that machine.
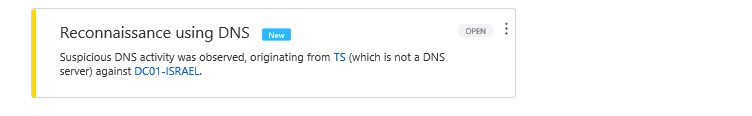
Let’s fake zone’s query from TS machine:
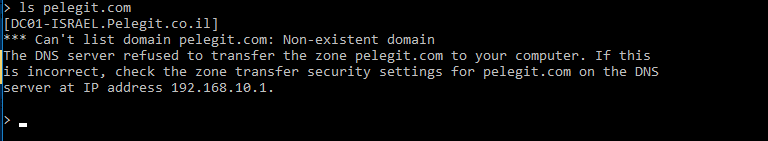
Reconnaissance evet created in the ATA:
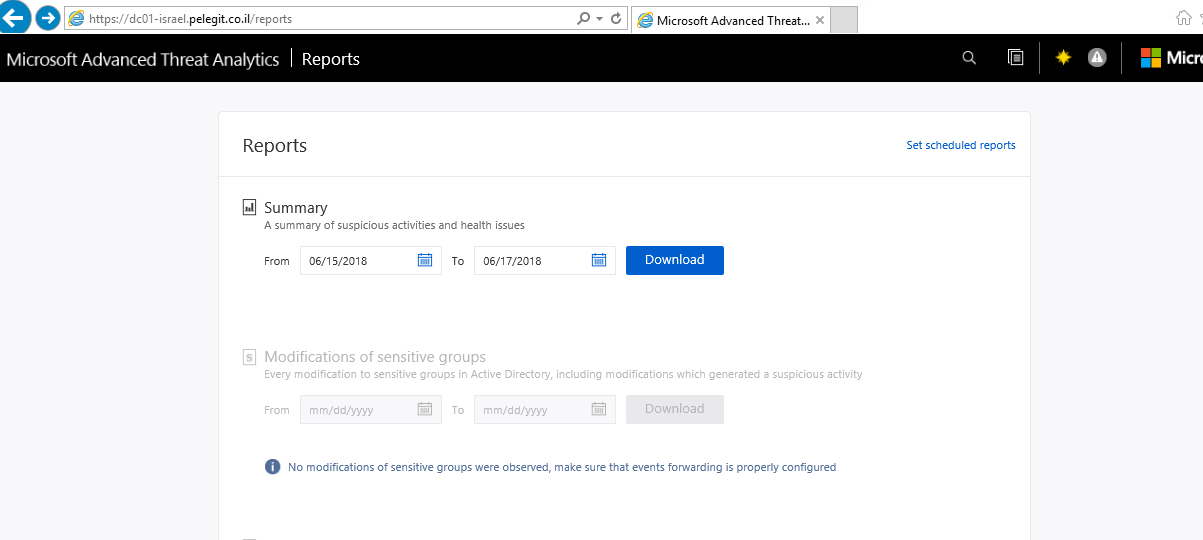
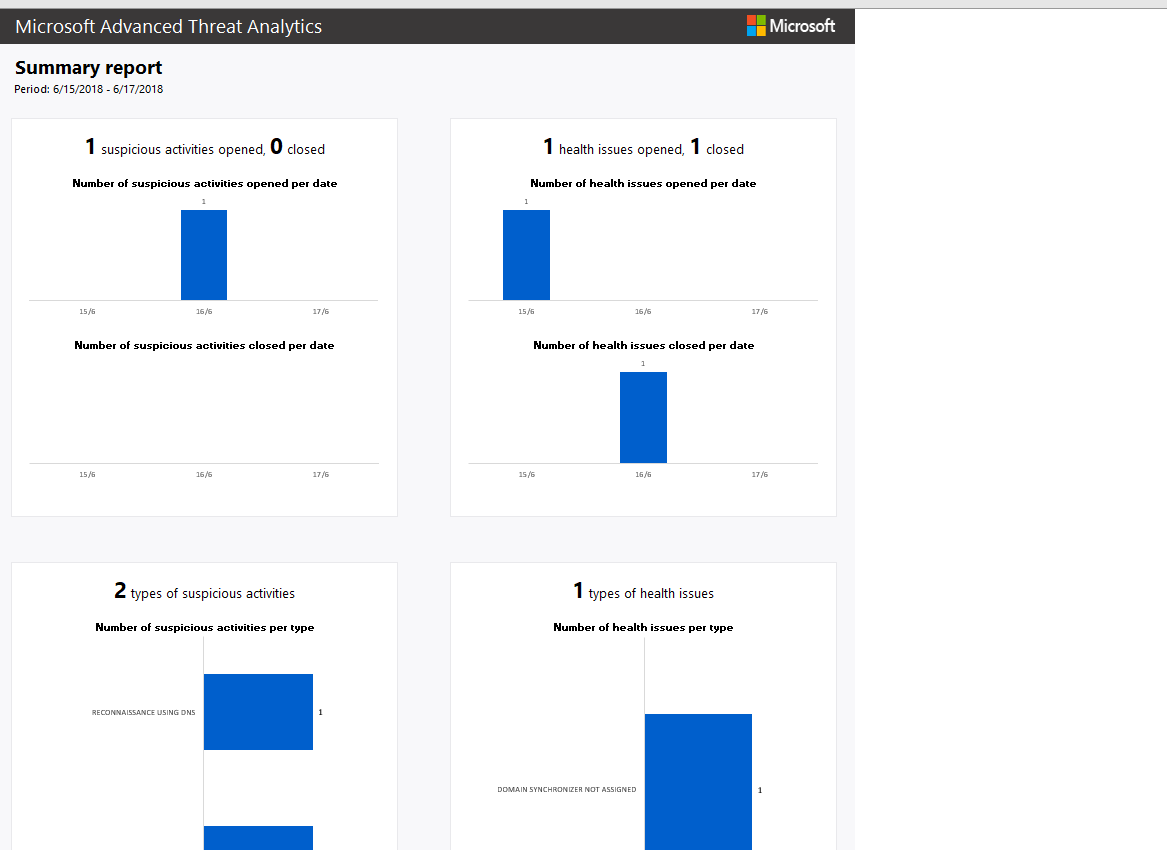
Reports:
A summary of suspicious activities and health issues:
Other available reports:
Modification of sensitive groups – sensitive modifications in admins groups.
Passwords exposed in cleartext – if there is a service that uses an LDAP query as non-secure protocol and sends a credential as cleat text.
Lateral movement paths to sensitive accounts – sensitive accounts that are exported via lateral movement paths
– You can schedule reports and send to your IT team once a week or daily.
Outcome:
Only one thing is bothering me, I have downloaded the Mimikatz on TS machine, but I haven’t got any alert, notification or Honeytoken activity, very disappointing, but in conclusion, we are talking about a good product which can be helpful for anybody. I pretty optimistic and confident that Microsoft improves the ATA and makes it better, just matter of time.
